Community articles — Portuguese (Brazilian)
Recent

O objetivo do experimento foi entender o princípio de funcionamento de um voltímetro, amperímetro, gerador de funções e osciloscópio digital, familiarizar-se com os principais controladores e ajustes dos instrumentos de bancada, e efetuar medições diversas, que serão utilizadas durante o semestre letivo.
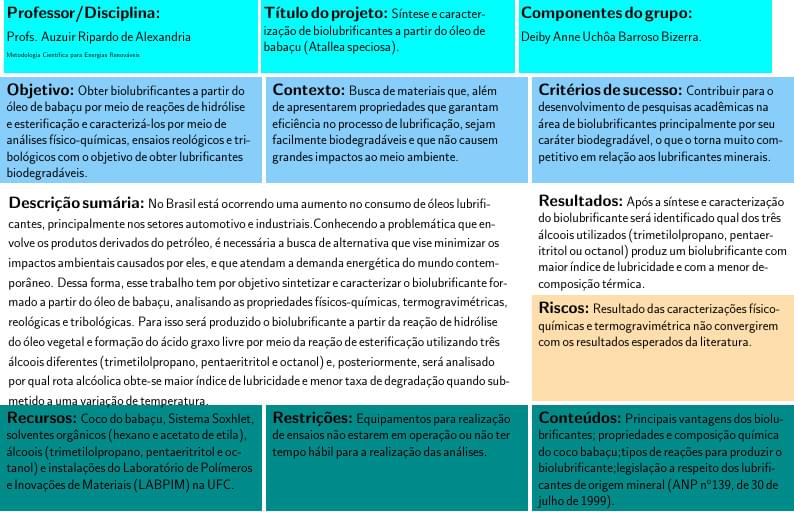
Trabalho 4 - Metodologia Científica
Estudo baseado na revista Ensinos do Reino da Editora Didaquê - Lição 2
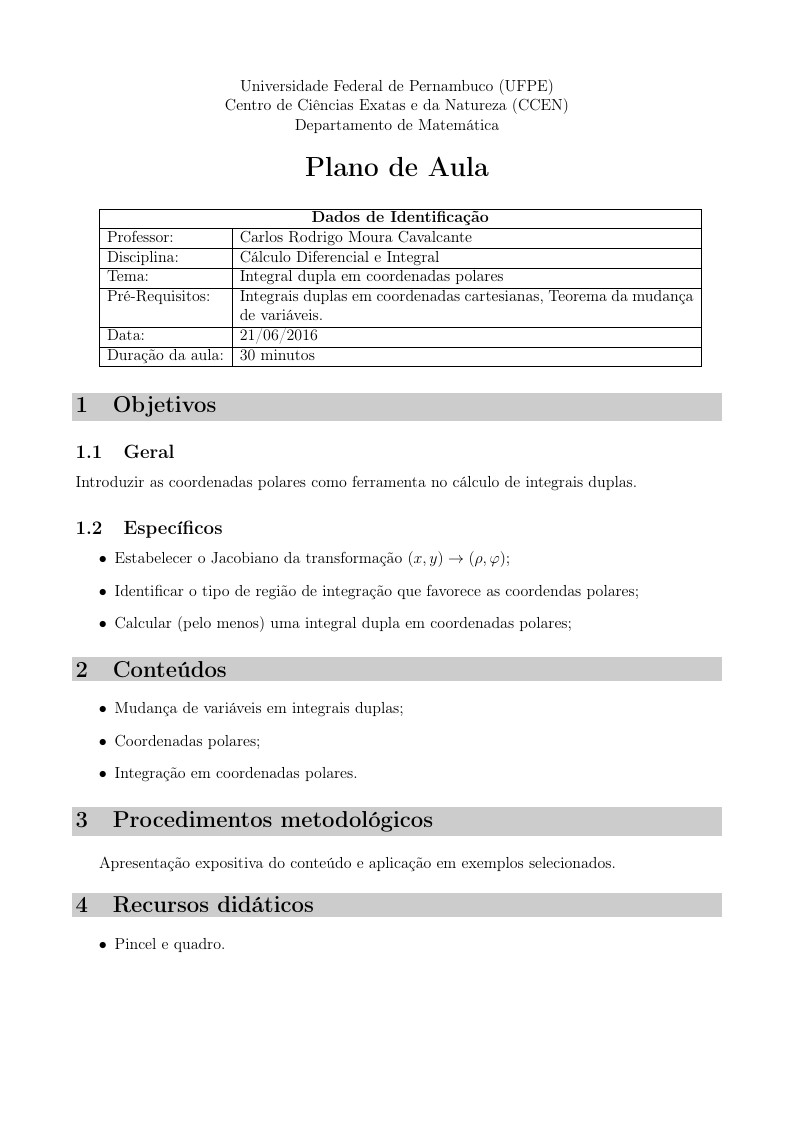
Integral dupla em coordenadas polares
Otimização do Sequenciamento da Produção em uma Linha de Placas Eletrônicas com Tempos de Setup Dependentes da Sequência
Trabalho experimental de determinação da Constante de Planck e do comportamento de Corpo Negro para um filamento de Tungstênio a partir da determinação de temperatura por resistência e por radiação eletromagnética.
Apresentação de Projeto de Crescimento da Igreja Presbiteriana Central de Coronel Fabriciano
Prática 9 de Tópicos de Física - CEFET
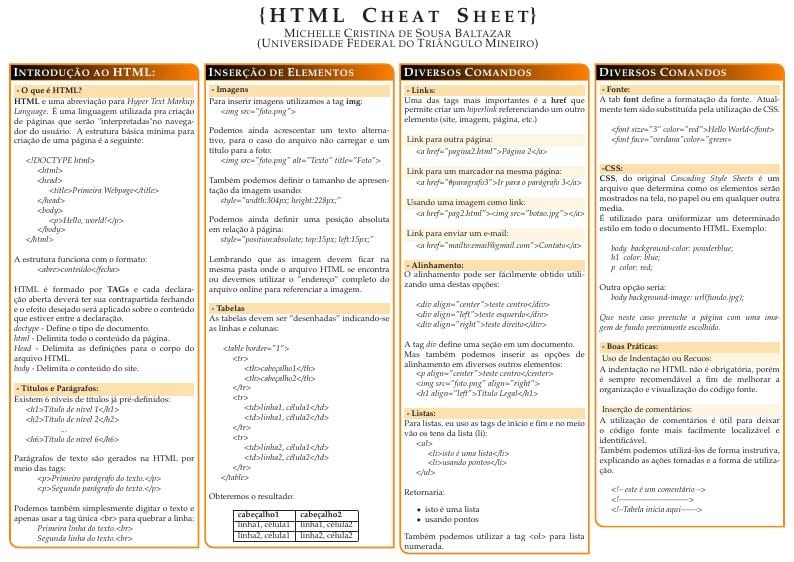
HTML Cheat Sheet Edited by Michelle Cristina de Sousa Baltazar baposter Landscape Poster This template has been downloaded from: http://www.LaTeXTemplates.com
\begin
Discover why over 25 million people worldwide trust Overleaf with their work.